Don't worry about VPNs and proxies, this is the difference
Don't worry about VPNs and proxies, this is the difference
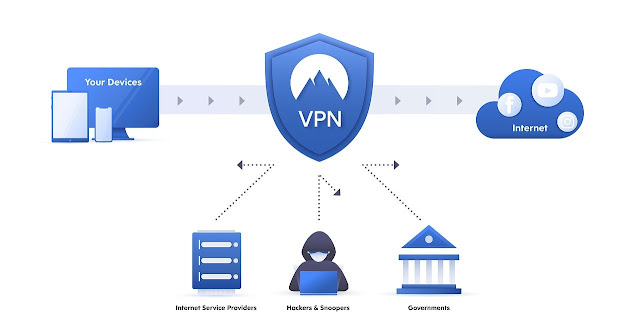
Virtual private networks (VPNs) are said to protect users. But most people are using proxies in the name of VPN. Therefore, it is very important for the user to always be clear about the actual VPN and proxy service.
Of course, both of these services are targeted at users' privacy, which allows you to access the Internet anonymously by hiding your IP address in various ways. But their working style is different.
Let's first discuss how VPN works. The VPN router brings all the internet activity connected to the user's WiFi network to its server to keep the user's identity secret. Computers and mobiles have VPN apps, which activate VPN apps on those devices to help keep the user's identity secret while using the Internet.
On the other hand, many of the devices we use contain services based on browser proxies. We are under the illusion that it is a VPN in the browser. VPNs on desktop or mobile phones are protecting the privacy of the entire device.
It protects the list of all kinds of Internet activities, file sharing apps, and email recipients in our browser. But browser-based proxies only provide protection for browser activity. The privacy and security of browser-based proxies are compromised. But these are very fast.
Browser-based VPN and proxy services have grown in popularity over the years. Various brands are also getting involved in it. But later it turned out to be just a proxy service. It had limited servers and poor encryption standards.
It appears to protect only IP data on sites opened in the Opera browser. It did not have the additional features of other desktop VPNs. VPN encrypts all Internet traffic coming from the device, whether it's a Netflix app or a torrent client. But proxies can't do that.
Mozilla is currently testing services like VPN for its Firefox browser. Firefox's private network is also a proxy service. Which many are misinterpreting as VPN. Firefox Proxy only encrypts data originating from the Firefox browser but not all operating systems.
In the third trial period of Firefox's private network, it offers more security than Proxy Services. But it also has some weaknesses. The project, partnered with Mozilla, is Cloudflare. It logs in user data during Firefox's private network sessions.
Although not a browser-based Microsoft Edge VPN, Windows Ten has a built-in VPN feature. Which can be used by enabling. It's not very effective, but Microsoft has been saying that it will gradually upgrade. So far no one was able to send in the perfect solution, which is not strange, except Google Chrome and Safari.
Speaking of VPNs, we should not miss the Tor Browser. It's not exactly a VPN, but it's not a proxy service. It relays with websites or connects users from scattered networks of nodes. VPNs provide encrypted routes for Internet traffic, while Tor encrypts traffic from nodes.
Its real name is 'The Onion Router. This protects the user's data from multiple levels of protection before crashing into the connected site. This is a good option to browse the internet secretly.
If you still find the VPN alternative a hassle and don't want to take any risks, you can contact the genuine VPN providers directly.
Is online gaming addiction?
As mobile access becomes easier, the popularity of video games is increasing. Nowadays, mobile products with different features are being made to play more games.
National-international level competitions are increasingly attracting video games, especially among the youth. However, whether video games are addictive or not is still a matter of controversy. Last August, when the Chinese government banned children under the age of 18 from playing video games, many supported it.
China has taken such steps saying that children are addicted to video games. The World Health Organization has also backed the Chinese government's decision. On January 1, the organization released a manual entitled 'International Classification of Diseases, which for the first time mentions an addiction called 'Gaming Disorder.
This manual is especially used by physicians and health organizations. Even 20 years ago, it was thought that such games would make players violent, but no such evidence has been found. While there needs to be a discussion, it's not just for parents who are fed up with old social interactions or children playing fortnight.
If you look at gaming not only as an addiction but also as a business, the business of gaming in the world has increased a lot. According to a consultancy called News, worldwide gaming revenue in 2020 will be 170 billion, or about 202 trillion rupees, which is more than the music or movie sector.
As psychologists change the definition of 'addiction', the notion that computer games can become addictive has developed. In the past, taking too much nicotine or morphine was defined as an addiction. But in the late 1990s, addiction began to be defined as drug addiction, or recreation, according to Run Nelson, a psychologist at the University of Copenhagen.
Over time, human habits have come to be defined as addictions, according to Mark Griffiths, a psychologist at Nottingham Trent University. Nowadays, it is not a matter of controversy as some people are addicted to gambling. However, he says that such topics can also lead to addiction to recreational activities.
He argues that with gaming, people can get addicted to their work or exercise, or even sex. However, apart from gambling and gambling, the World Health Organization (WHO) has defined gaming as an addiction. Players with gaming disorders are also affected by other aspects of life due to their addiction.
Psychologists also define games as people who have no offline relationships, work, or sleep. On top of that, there is a quarrel with the family. Some gamers say that they are addicted and have struggled to break free.
Hillary Cass, director of the Game-Addiction Clinic in Seattle, USA, says most patients who come to her are students who have been expelled from school or university. On top of that, she said, most of the patients are men.
While all these discussions are going on, the issue of gaming addiction is still in dispute. On the one hand, the habit of playing a lot of games is considered to be addictive, while on the other hand, psychologists think that there are not many symptoms required for addiction.
Some have argued that playing games as a way to relax one's mind while doing one-on-one activities can be as healthy as other habits, including exercise. However, most gamers experience depression or anxiety.
A new dimension of the game
While gaming is being defined by psychologists, in terms of business, the gaming sector is flourishing day by day. In the past, players used to buy video games and play them, and developers did not even know how the customer was playing them.
But today that process has changed. Most games are free to play, but developers make money through in-game purchases. According to News, 73% of gaming revenue in 2020 came from free games.
In such a game, the player can download and play the game for free, but he has to pay for raising his level or other activities within the game. In this way, designers, with the help of psychologists, develop games on how to increase game playtime.
Activities such as giving various rewards for the person playing the game, giving surprise gifts, etc. attract more people and they become more engrossed in the game. Another way is to alert the player.
In this case, when the player does not play for a long time, the game acts as a notification. In a virtual pet game called 'Adopt Me', if the player does not play the game for a while, notifications like 'Why do you ignore me?'
Another way is for the player to purchase playing time. Like most of us have played a game called Candy Cross. In which we have to wait for half an hour after the end of playing live for life or we have to buy life through virtual coins. This is a way to increase user playtime.
One of the UK in 2018 Na Player spent 2,600 a day to add life to Candy Cross. That's how game developers make their living.
But for most players, the effects of this psychological engineering seem limited. Not all players purchase in-game in this way. Of course, it is difficult to get definite data. But based on the international media, 70 percent of Apple's App Store revenue comes from games.
This does not mean buying by many players. But because of the players who spend a lot, this percentage is very high. On the one hand, there is talk of increasing its addiction, on the other hand, there are also voices about its professionalism. Whether or not to call online games addictive is still a matter of controversy.
This issue has become a matter of concern not only for China but also for the politicians of the world. In Belgium and the Netherlands, there is talk of regulating gambling in the same way as gambling.
The UK, the world's fifth-largest gaming market, has made it a rule to protect gamers under the age of 18. Parliamentarians have repeatedly raised the issue of shutting down such gaming platforms in the Parliament of Nepal.
Think of it this way: Remote Desktop and Virtual Desktop
Lately, we have become more dependent on online. In this way, we are working by accessing office laptops and computers from home. For that, we are using many technologies.
Here we are giving information about remote desktops and virtual desktops.
What is a remote desktop?
The remote desktop program allows you to access and interact with a computer located in another location. You can physically access it from another location, just like sitting in front of a desktop.
When it was not possible to use hardware during Covid-19, the use of virtualization tools like remote desktops proved to be very useful.
Remote desktop software is generally available on all types of operating systems. The client computer is enabled to connect the host computer to the Internet.
The host device displays the software and operating system on the client device. By capturing client device mouse and keyboard inputs and sending them back to the host machine, remote desktop software allows individuals to interact with their normal desktop.
Remote Desktop: Advantages and disadvantages
The main advantage of remote desktop software is that you can work from anywhere where the internet is available. If you have a computer with an internet connection, you can easily access any computer.
Another advantage of remote desktop protocols is their security. Users can securely access their documents. All files have encrypted connections.
Instead of buying multiple licenses, businesses can give employees access to business tools by setting up remote desktops. But delivering remote desktop services on a large scale requires powerful software as well as a strong network connection.
What is a virtual desktop?
Although virtual desktops and remote desktops offer the same features, there are some significant differences. Virtual Desktop provides a pre-configured image of the operating system or application. On the Internet, any endpoint device can be used for laptop, tablet, or smartphone virtual desktop access.
On-premises or hosted in the cloud, virtual desktops are more complex than remote desktops. Virtual Desktop lets users access their desktop and applications from anywhere on any type of endpoint device. IT organizations can deploy, manage and monitor these desktops from the data center.
Virtual desktop: advantages and disadvantages
Security: All data is stored in the data center, not on the endpoint device. Even if the endpoint device is stolen, there is no data on the device.
Convenience: IT administrators can quickly and easily allocate virtual desktops to users, without the need for expensive physical machines.
Cost: Virtual desktops have much lower physical equipment and maintenance costs.
Since all processing shifts from personal devices to virtual desktop servers, many PCs do not require upgrades but require extensive investment in server hardware, storage, and network devices.



Do you know what bitcoin casino sites are offering?
ReplyDeleteAre you looking for a casino that offers live dealer games? Well, you'll probably know 온카지노 about these online 코인카지노 코드 casino What is the หาเงินออนไลน์ best 바카라 사이트 유니벳 Bitcoin gambling site?How do you use 나비효과 Bitcoin for betting?