What is spectrum or frequency? This is easy to understand
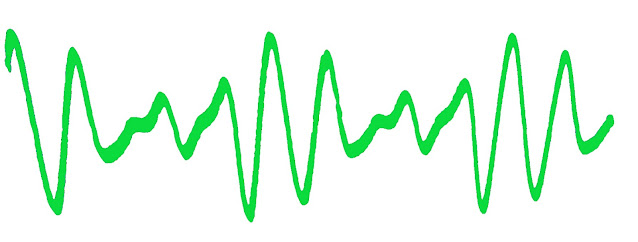
What is spectrum or frequency? This is easy to understand Although the term spectrum sounds unfamiliar to many and is very technical, most people are exposed to it every day. It has become a very important part of our daily lives. Of course, the question arises, what is the frequency? And how does it affect the lives of ordinary people? Frequency is something that cannot be seen with the naked eye. It is also called an electro magnetizing field. Whether it is remote, micro web, mobile, or radio, we are coming in contact with it every day through some means. Frequency or spectrum is the amount of radiation energy that surrounds the earth. The sun is the main source of electromagnetic radiation. It also receives energy from stars and galaxies. Apart from this, such energy is also generated from the radioactive elements that are buried under the ground. Some of the frequencies we call spectrum or radiation are very useful. Which does us no harm. Through which we can listen to the radio. W...








